The current cybersecurity landscape resembles a sea full of sharks that are so hungry that they’ve started to go after small fish—small and medium-sized businesses. It’s no wonder that those who can afford it are increasing their cybersecurity budgets. They have to in order to address growing threats like ransomware and business email compromise (BEC).
This is driving the growth of the information security and risk management market from $172.5 billion in 2022 to $267.3 billion in 2026.
While the willingness to throw money at security threats is commendable, the results often fall short of expectations. Use the five tips below to maximize the impact of each dollar you spend on cybersecurity.

5 Ways to Maximize Your Cybersecurity Budget
1. Take Full Advantage of Existing Capabilities
Giving a soldier a bunch of extra weapons won’t make them any more capable of repelling an enemy attack if they don’t know how to use them correctly. Likewise, an organization doesn’t become more resistant to cyberattacks by layering security protections on top of each other.
In fact, an overabundance of tools is a far more common obstacle in threat detection and remediation than a lack of tools for remediating cybersecurity threats. This was revealed by a survey conducted at the June 2022 RSA Conference.
Unfortunately, this obstacle is common.
According to the third-annual Oracle and KPMG Cloud Threat Report 2020, 78 percent of organizations use more than 50 discrete cybersecurity products to address security issues. What’s more, 37 percent use over 100 cybersecurity products.
It’s safer—and certainly more cost-effective—to take full advantage of existing cybersecurity capabilities.
Example
Many organizations that spend money on a Microsoft 365 subscription (because they rely on the Microsoft Office product line) largely ignore the numerous Microsoft Security products that are included with it.
This includes features like:
Why is it such a problem to have too many security tools?
Because they may generate an overwhelming number of confusing alerts, compromising the ability of cybersecurity professionals to identify alerts that do matter and respond to them. Fortunately, the solution is simple: get rid of the tools you don’t need.
While you’re at it, you should also review your existing licenses and vendor agreements. The IT landscape is constantly evolving, so it’s possible that better options are now available.
Your own IT needs may be different as well. So, stop wasting your cybersecurity budget by paying for something you don’t need anymore.
Takeaway: The more tools you add to the mix may weaken your overall defense posture by creating more room for confusion and misconfiguration.
2. Strengthen the Weakest Links First
The strength of the cybersecurity chain is always determined by its weakest link. What this means is that you can implement, for example, the most sophisticated intrusion detection system. But your overall ability to resist cyber attacks will remain the same… unless it stands on a rock-solid cybersecurity foundation.
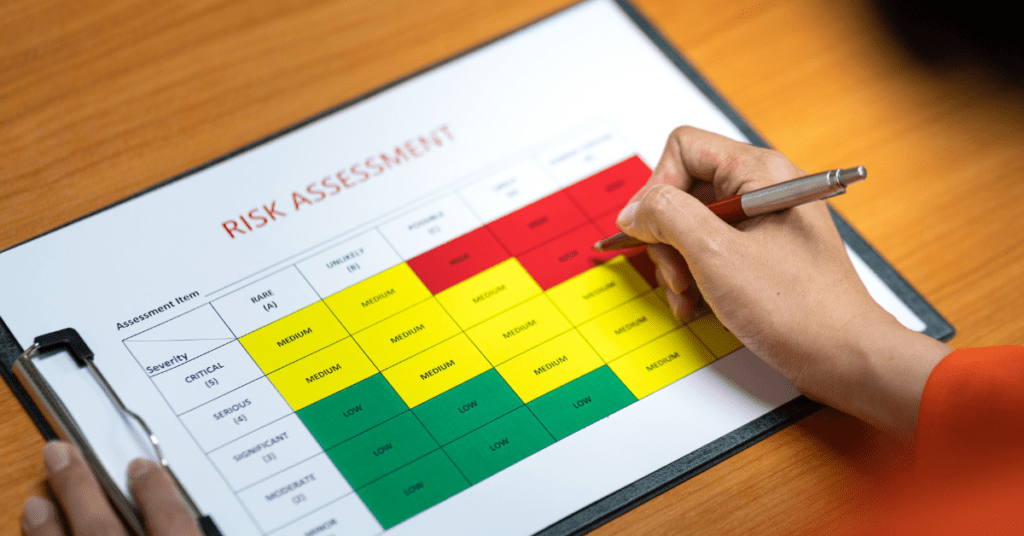
To determine which threats you should focus on, we recommend you conduct a cybersecurity risk assessment to identify, assess, and prioritize risks to your information and information systems.
The outcome of your cybersecurity risk assessment should be a list of risks and their potential impact on your organization. By also considering their likelihood, it’s possible to determine their priority using a risk matrix.
Any risk that has a fairly high probability of occurring and the potential to cause a lot of harm should be prioritized and addressed before risks that are unlikely to occur or cause a lot of harm or both.
Common High-priority Risks
A good example of a high-priority risk is poor password hygiene, which plays a role in 88 percent of data breaches.
Similarly, unpatched vulnerabilities are responsible for one in three incidents, so it’s crucial for all systems, applications, and devices to be fully updated.
3. Don’t Get Swayed by the Latest Cybersecurity Trends
Every year, new cybersecurity trends emerge which influence how organizations allocate their IT budgets. Since the COVID-19 pandemic disrupted established work routines, hybrid work security has been a topic of many C-level discussions.
The same can be said about cloud security threats or Internet of Things (IoT) vulnerabilities. This has caused many organizations to hastily bolster their defenses by investing in a variety of different solutions.
You should pay attention to these trends. However, don’t let them control over your strategy and cybersecurity budget.
Keep in mind that every organization is unique. Because of this, the risks it needs to address are just as unique. To address this challenge, develop a detailed cybersecurity plan.
Discover 16 essential cybersecurity controls your small business needs to reduce risk and avoid costly damages associated with a cyberattack.
4. Outsource to Get the Most from Your Cybersecurity Budget
In the United States alone, there are over 700,000 unfilled cybersecurity positions available. The cybersecurity skills shortage is massive, and its impact on organizations is worse.
According to the Fortinet 2022 Cybersecurity Skills Gap Global Research Report, 80 percent of organizations suffered one or more breaches that were attributed to a lack of cybersecurity skills and/or awareness.
Most small and medium-sized organizations that don’t outsource at least some of their cybersecurity operations to a managed security services provider (MSSP) are wasting money. Why?
Because they’re not taking advantage of the greater economies of scale from which all MSSPs benefit. They can help you get the most out of your cybersecurity budget!

Learn the financial impact of cyber threats on your business’s data. Plus, unlock the financial implications of in-house vs. outsourced cybersecurity.
Organizations can easily outsource their cybersecurity operations to an MSSP, like Teal. This allows them to gain the enterprise-level cybersecurity they need at a price they can afford.
Our integrated cybersecurity is tailored to your organization’s needs. We provide robust protection seamlessly implemented by certified cybersecurity experts.
5. Measure Your Return on Investment
Simply throwing money at security threats is not the best approach to cybersecurity. You need to measure its effectiveness. If you don’t, your cybersecurity investments can lead to money wasted or unintentional vulnerabilities.
According to Comparitech, 75% of cyberattacks in 2020 used vulnerabilities that were at least two years old. This means that many organizations are failing to address known weaknesses in their systems.
Additionally, more than 11% of vulnerabilities have a critical score (9.0–10.0 on the CVSS scale) – indicating a high severity that should be quickly mitigated.
That means, knowing whether your cybersecurity plan is working efficiently is key.
A key performance indicator to keep an eye on when measuring the effectiveness of cybersecurity investments is the number of times an attacker has breached your network. You can also monitor:
- How long security threats go unnoticed.
- How long it takes you to respond to them.
- & more
Remember, create a comprehensive plan and follow through with it… paying close attention to the details.

Get the Most from Your Cybersecurity Budget
If your goal is to spend every dollar of your cybersecurity budget as efficiently as possible, then you need to:
- Be sure you have the foundational security measures. Track your defense progress regularly. This will help inform your future decision-making activities.
- If you find that your in-house skills are lacking (or your team doesn’t have the bandwidth to take on the cybersecurity challenges your business faces), consider outsourcing to an MSSP.
Outsourcing to a managed IT service provider is the best way to close the cybersecurity skills gap at an affordable cost – giving you peace of mind.
Teal offers responsive and secure managed IT services to SMBs nationally.
If you’re interested in learning about our premier IT consulting, contact a Teal business technology advisor today.